Projects
Current Projects
IoTGuard: IoT Security in Smart Homes, Production, and Sensitive Infrastructure

The IoTGuard project, in collaboration with partners TU Darmstadt, Intel, Kobil, and IoT-Venture, develops AI-driven security for smart homes. Despite IoT excitement, challenges in device diversity and adversarial attacks persist. IoTGuard focuses on addressing these issues, emphasizing smart home security, distributed learning, and context-based attack detection. Insights are expected to apply in critical environments beyond smart homes ❯ More
SPOQ Project: Ending Plagiarism in Global Supply Chains

The German economy suffers more than 50 billion euros in damage from product and brand piracy each year. The EU market surveillance authorities classified 97 percent of the counterfeits recorded as goods with serious risks. Production and logistics companies are powerless against plagiarism: Globally, there is no cross-industry, cross-border approach to product identity verification ❯ More
CROSSCON: Cross-platform Open Security Stack for Connected Devices

The main challenge for IoT developers is the lack of a unified security solution that can work across a variety of different devices. To bridge this gap, the CROSSCON project pools the expertise of 11 research teams throughout Europe to develop a new open and vendor-independent security stack for connected devices. The CROSSCON security stack provides a consistent security baseline across a whole IoT system. ❯ More
Ransomware Detection with Machine Learning

Data has become more critical than ever in today's digital transformation era. The amount of data we produce daily is astonishing — every day, hundreds of millions of people are taking photos, making videos, and exchanging messages. Given such trends, the importance of database security is hard to overestimate: The rapid growth of the data volume stored in the databases in cloud environments and enterprise data centers makes them attractive attack targets. ❯ More
Smarter Contracts - Vulnerability Detection using Deep Neural Networks
Smart Contracts are computer programs that execute on a blockchain. The nature of blockchains allows one to run Smart Contracts in a trustless and decentralized environment. In this project, we demonstrate the effectiveness of Deep Neural Networks in the domain of Smart Contract vulnerability detection. ❯ More
Private AI Collaborative Research Institute
Intel, in collaboration with Avast and Borsetta, launched the Private AI Collaborative Research Institute to advance and develop technologies in privacy and trust for decentralized AI. ❯ More
Past Projects
Liveness Detection for Facial Authentication Systems
Facial authentication systems are being used globally to ease the authentication process of various applications. Attackers have become interested in bypassing such systems in order to gain illicit access to restricted areas. Aggravatingly, past research has shown that state-of-the-art facial authentication systems are vulnerable to simple attacks. This project works on a Machine Learning based solution that detects the presence of attacks and thereby provides resilience for existing facial authentication systems. ❯ More
Behavioral User Authentication on Mobile Devices using Machine Learning

In this project, we develop zero-effort authentication methods for mobile devices that leverage user behavioral characteristics to identify authorized users. It appears that physical behavioral patterns, such as a way a person is typing, tapping, swapping, scrolling, navigating and even holding a mobile device, are user-specific and can be used for authentication. We leverage established Machine Learning methods and demonstrate that they can effectively distinguish different users by analyzing data collected from movement sensors ❯ More
Privacy – Mobile Contact Discovery
Contact discovery allows users of mobile messengers to conveniently connect with people in their address book. In this work, we demonstrate that severe privacy issues exist in currently deployed contact discovery methods. ❯ More
eSano- An eHealth Platform for Internet- and Mobile-based Interventions

Internet- and mobile-based interventions (IMIs) can help improve health care by offering location- and time-independent services. ❯ More
(Federated) Machine Learning for Risk Detection on Mobile Platforms
The importance of security and protection of private information on mobile devices has increased in recent years due to the widespread use of these devices. This lead to the intensive use of mobile platforms for security-critical tasks, such as online banking, mobile payments, healthcare applications or business-related activities. On another hand, mobile platforms became attractive attack targets, since they store and process a significant amount of security-critical information, such as authentication credentials, payment information, and access tokens. ❯ More
TraceCORONA - Anonymous contact tracing for pandemic response
TraceCORONA is designed to be not only a tracing app, but a system concept that allows the TraceCORONA tracing component as well as other possible tracing apps to integrate into a secure health platform for private healthcare-related services over a well-defined secure interface. ❯ More
SIMPL: Secure Internet of Things Management Platform
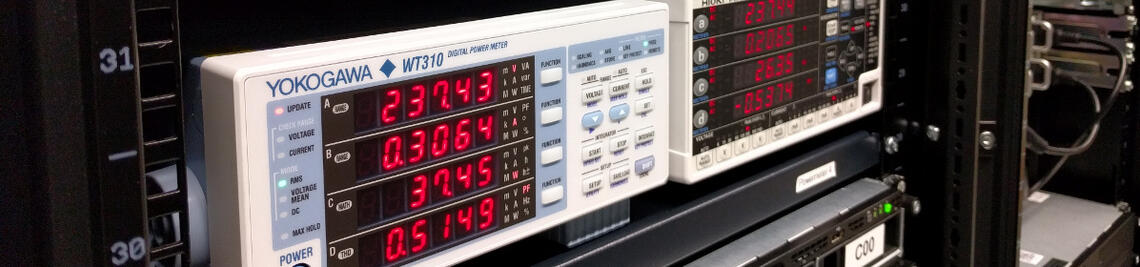
The proliferation of IoT devices is increasing at a fast pace,whether for private or business use. However, despite their growing popularity, their safe operation is often not guaranteed. To tackle the security challenges of modern IoT environments, the German Federal Ministry of Education and Research is funding the SIMPL project in order to support research in this area. ❯ More